In the rapidly evolving world of technology, securely connecting remote IoT devices through P2Psh on Android for free has become a critical need for both individuals and businesses. The Internet of Things (IoT) continues to expand, bringing convenience but also raising concerns about security and privacy. This article aims to provide a detailed exploration of how you can safely and securely connect IoT devices using P2Psh on Android without incurring additional costs.
As more devices become interconnected, ensuring that these connections remain secure is paramount. Whether you're a tech enthusiast, a small business owner, or simply someone looking to protect your personal data, understanding the nuances of secure IoT connections is essential.
This guide will walk you through the process of setting up secure connections, highlight the best practices, and provide actionable tips to safeguard your IoT ecosystem. By the end of this article, you'll have the knowledge and tools necessary to ensure your IoT devices remain protected while maintaining seamless connectivity.
Read also:Unraveling The Depths Of Shakespeares Sonnet 73 A Paraphrase Exploration
Table of Contents
- Introduction to IoT
- Understanding P2Psh
- Android as an IoT Platform
- Securing Remote IoT Connections
- Benefits of Free Secure Connections
- Step-by-Step Guide to Securely Connect IoT Devices
- Common Security Challenges
- Tools and Applications for IoT Security
- Best Practices for IoT Security
- Future of IoT Security
- Conclusion
Introduction to IoT
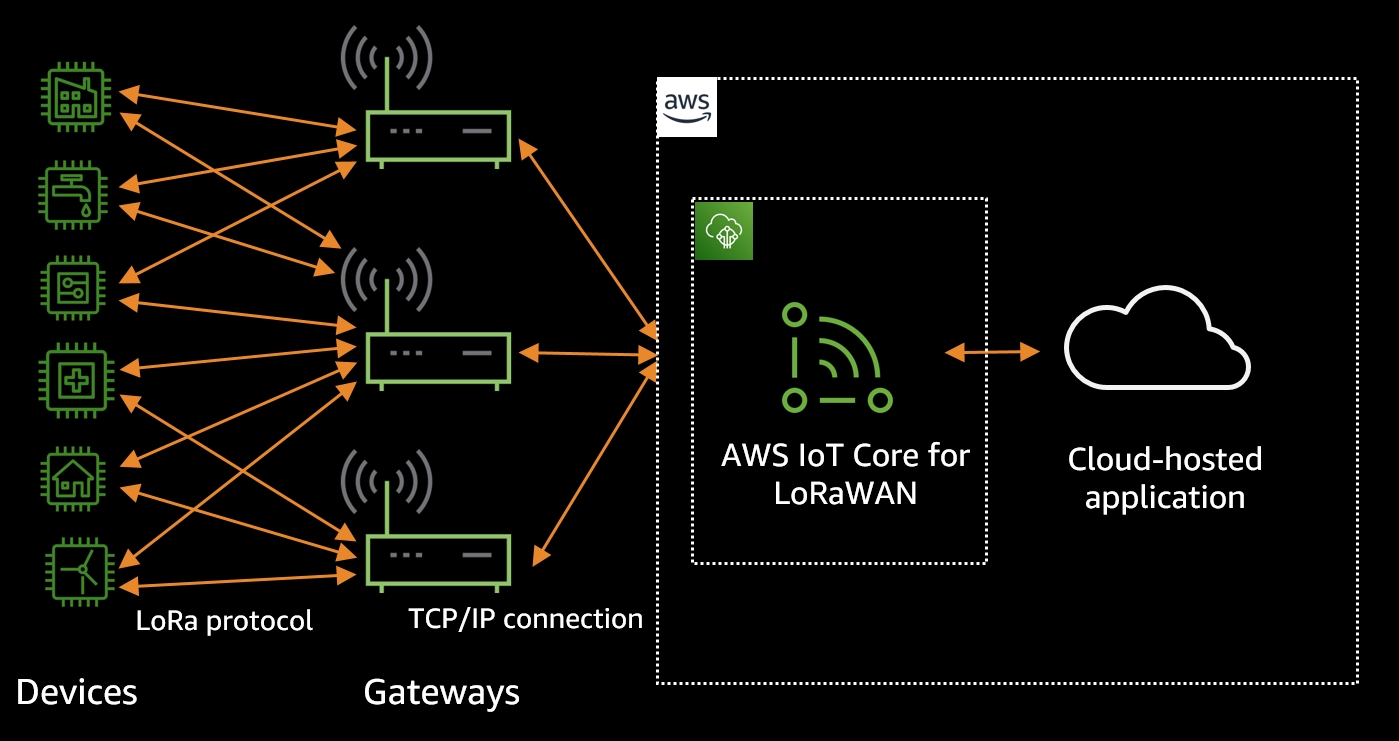
The Internet of Things (IoT) refers to the network of physical devices embedded with sensors, software, and connectivity, enabling them to exchange data and perform various tasks. From smart home appliances to industrial machinery, IoT devices have revolutionized the way we interact with technology.
Importance of IoT in Modern Technology
IoT plays a crucial role in enhancing efficiency, reducing costs, and improving overall quality of life. By automating processes and providing real-time data, IoT devices empower businesses and individuals to make informed decisions.
Growth of IoT Devices
According to a report by Statista, the number of IoT devices worldwide is projected to reach over 30 billion by 2025. This rapid expansion highlights the increasing reliance on IoT technology across various sectors.
Understanding P2Psh
P2Psh (Peer-to-Peer Sharing) is a protocol that facilitates direct communication between devices without the need for a central server. This approach offers several advantages, including reduced latency and enhanced security.
How P2Psh Works
- P2Psh establishes a direct connection between two devices.
- Data is transmitted securely without intermediaries.
- Devices can communicate even when located in different networks.
Advantages of Using P2Psh
By leveraging P2Psh, users can achieve faster data transfer rates and maintain privacy, as no third-party servers are involved in the communication process.
Android as an IoT Platform
Android has emerged as a leading platform for IoT development due to its open-source nature and extensive developer community. With a wide range of tools and resources available, Android provides an ideal environment for building and deploying IoT applications.
Read also:Mia Z Girth Master The Ultimate Guide To Understanding Her Impact And Achievements
Key Features of Android for IoT
- Support for multiple communication protocols.
- Integration with cloud services for data storage and analysis.
- Compatibility with a variety of hardware components.
Popular Android-Based IoT Projects
From smart home automation to wearable health monitors, Android-powered IoT projects continue to push the boundaries of innovation. These projects demonstrate the versatility and potential of Android in the IoT space.
Securing Remote IoT Connections
Securing remote IoT connections is vital to protect sensitive data and prevent unauthorized access. By implementing robust security measures, users can ensure their IoT devices remain safe and reliable.
Encryption and Authentication
Using encryption protocols and strong authentication mechanisms is essential for safeguarding IoT communications. This includes employing SSL/TLS for data encryption and multi-factor authentication for added security.
Regular Software Updates
Keeping IoT devices up to date with the latest software patches and security updates is crucial. Manufacturers and developers must prioritize releasing timely updates to address vulnerabilities.
Benefits of Free Secure Connections
Accessing secure IoT connections for free offers numerous advantages, including cost savings and increased accessibility. By utilizing open-source tools and community-driven solutions, users can achieve secure connectivity without incurring additional expenses.
Cost-Effective Solutions
Free secure connection methods eliminate the need for expensive proprietary software, making IoT technology more accessible to a broader audience.
Community Support
Open-source projects often benefit from active communities that provide support, share knowledge, and contribute to ongoing development efforts.
Step-by-Step Guide to Securely Connect IoT Devices
Follow this step-by-step guide to securely connect your IoT devices using P2Psh on Android:
Step 1: Install Necessary Applications
Begin by downloading and installing the required applications on your Android device. Ensure these applications are from trusted sources and have been verified for security.
Step 2: Configure P2Psh Settings
Access the settings menu of your P2Psh application and configure it to establish secure connections. Customize encryption protocols and authentication methods as needed.
Step 3: Connect Devices
Pair your IoT devices with your Android device using the P2Psh protocol. Follow the on-screen instructions to complete the connection process.
Common Security Challenges
Despite the advancements in IoT technology, several security challenges persist. Addressing these challenges is essential to maintaining the integrity of IoT ecosystems.
Data Privacy Concerns
Protecting user data from unauthorized access and ensuring compliance with privacy regulations remain significant challenges in the IoT landscape.
Device Vulnerabilities
Many IoT devices come with inherent vulnerabilities that can be exploited by malicious actors. Regular security assessments and updates are necessary to mitigate these risks.
Tools and Applications for IoT Security
A variety of tools and applications are available to enhance IoT security. These tools provide features such as intrusion detection, network monitoring, and vulnerability scanning.
Recommended Tools
- Snort: An open-source intrusion detection system.
- Wireshark: A network protocol analyzer for monitoring and analyzing traffic.
- OpenVAS: A comprehensive vulnerability scanning solution.
Application Integration
Integrating security tools with IoT applications can streamline the management and monitoring of device networks, ensuring optimal protection.
Best Practices for IoT Security
Adopting best practices is crucial for maintaining the security of IoT devices and networks. Follow these guidelines to enhance your IoT security posture:
Network Segmentation
Separate IoT devices from other network components to limit potential damage in case of a breach.
User Education
Educate users about the importance of strong passwords, regular updates, and recognizing phishing attempts to reduce the risk of security incidents.
Future of IoT Security
The future of IoT security lies in advancements such as artificial intelligence, blockchain technology, and quantum cryptography. These innovations hold the potential to revolutionize the way we approach IoT security, offering more robust and scalable solutions.
Emerging Technologies
AI-driven security systems can detect anomalies and respond to threats in real time, while blockchain technology provides a decentralized and tamper-proof method for securing data transactions.
Regulatory Developments
As IoT adoption grows, governments and regulatory bodies are increasingly focusing on establishing standards and guidelines to ensure the security and privacy of IoT devices.
Conclusion
In conclusion, securely connecting remote IoT devices using P2Psh on Android for free is both achievable and essential in today's interconnected world. By following the steps outlined in this guide and adhering to best practices, you can ensure your IoT ecosystem remains protected and reliable.
We invite you to share your thoughts and experiences in the comments section below. Additionally, consider exploring our other articles for more insights into IoT technology and security. Together, we can build a safer and more connected future.