Connecting remote IoT devices through P2Psh Android securely is a critical aspect of modern technology implementation. As more devices become interconnected, ensuring robust security measures has never been more important. This article will delve into the intricacies of secure IoT connections, focusing on peer-to-peer (P2P) networking and Android-based solutions.
With the rapid advancement of the Internet of Things (IoT), the demand for secure communication between devices has surged. Whether it's for personal or industrial use, maintaining data integrity and privacy is paramount. This guide aims to provide practical insights into securing IoT connections, particularly for Android-based systems.
Throughout this article, we will explore various aspects of remote IoT connectivity, including the use of P2Psh technology. By the end of this guide, you'll have a deeper understanding of how to safeguard your IoT devices and ensure seamless communication in a secure environment.
Read also:Comprehensive Guide To Dr Jeffs Canine Care Expert Tips For Your Furry Friend
Table of Contents
- Introduction
- Understanding IoT and Its Importance
- What is P2Psh and How Does It Work?
- Integrating P2Psh with Android
- Security Challenges in IoT
- Steps to Securely Connect Remote IoT Devices
- Best Practices for IoT Security
- Tools and Technologies for Enhanced Security
- Ensuring Data Privacy in IoT
- Future Trends in IoT Security
- Conclusion and Call to Action
Introduction
The Internet of Things (IoT) has transformed the way we interact with technology, enabling devices to communicate and exchange data seamlessly. However, as the number of connected devices grows, so does the risk of security breaches. Securely connecting remote IoT devices, especially through P2Psh Android, requires a comprehensive approach that addresses potential vulnerabilities.
Understanding IoT and Its Importance
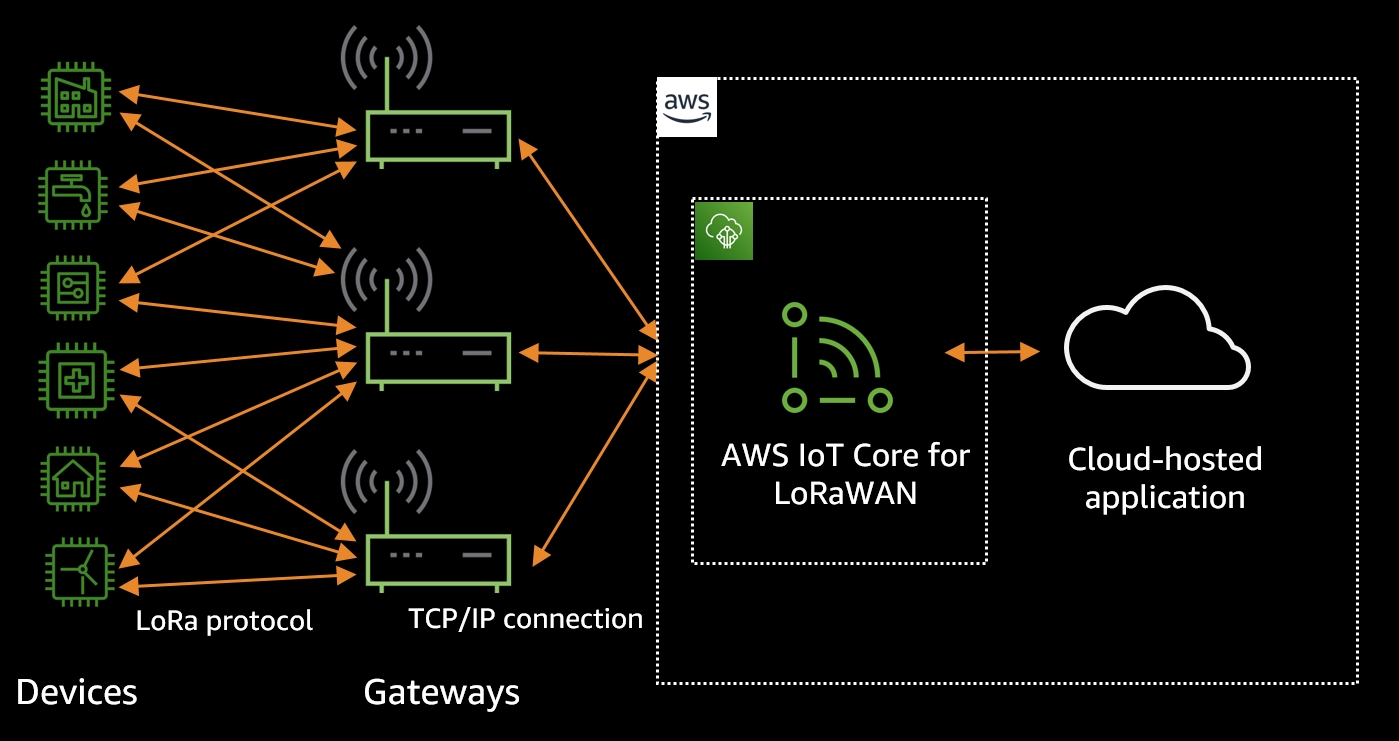
The Internet of Things (IoT) refers to the network of physical devices embedded with sensors, software, and connectivity, enabling them to exchange data. IoT plays a crucial role in enhancing efficiency, reducing costs, and improving user experiences across various industries.
For instance, in smart homes, IoT devices can automate tasks, optimize energy usage, and enhance security. In healthcare, IoT enables real-time monitoring of patients, leading to better health outcomes. However, the widespread adoption of IoT also raises concerns about data security and privacy.
Key Components of IoT
- Sensors: Devices that collect data from the environment.
- Connectivity: The ability of devices to communicate with each other.
- Data Processing: Analyzing and interpreting collected data.
- User Interface: Providing users with meaningful insights and control.
What is P2Psh and How Does It Work?
P2Psh is a peer-to-peer (P2P) technology that facilitates direct communication between devices without relying on centralized servers. This approach offers several advantages, including reduced latency, improved scalability, and enhanced security. By eliminating the need for intermediaries, P2Psh ensures that data is transmitted directly between devices, minimizing the risk of unauthorized access.
Advantages of P2Psh
- Decentralized Architecture: Reduces dependency on central servers.
- Enhanced Security: Data is encrypted and transmitted directly between devices.
- Improved Efficiency: Lower latency and higher bandwidth utilization.
Integrating P2Psh with Android
Android devices are increasingly being used as control hubs for IoT ecosystems. Integrating P2Psh with Android allows users to securely connect and manage remote IoT devices from their smartphones or tablets. This integration leverages Android's robust security features and extensive developer community to create innovative solutions.
Steps to Integrate P2Psh with Android
- Install the P2Psh library on your Android device.
- Configure the device to act as a P2P node.
- Establish secure communication channels with remote IoT devices.
- Monitor and manage connected devices through the Android app.
Security Challenges in IoT
Despite its numerous benefits, IoT faces several security challenges that must be addressed to ensure safe and reliable operation. These challenges include unauthorized access, data breaches, and device vulnerabilities.
Read also:Discover Trapp Family Lodge In Stowe Vt A Vermont Getaway
According to a report by Gartner, the global spending on IoT security is expected to reach $7.4 billion by 2024, highlighting the growing importance of securing IoT ecosystems.
Common IoT Security Threats
- Malware Attacks: Infecting devices with malicious software.
- Denial of Service (DoS): Overloading devices with traffic to disrupt operations.
- Data Interception: Eavesdropping on communication channels to steal sensitive information.
Steps to Securely Connect Remote IoT Devices
Securing remote IoT connections involves implementing a combination of hardware, software, and network-level measures. Below are some essential steps to ensure secure communication between devices:
Implementing Encryption
Encryption is a fundamental aspect of IoT security. By encrypting data transmitted between devices, you can prevent unauthorized access and ensure data integrity. Common encryption protocols used in IoT include AES, RSA, and TLS.
Using Secure Authentication
Authentication ensures that only authorized devices and users can access the IoT network. Implementing multi-factor authentication (MFA) and digital certificates can significantly enhance security.
Best Practices for IoT Security
Adhering to best practices is crucial for maintaining the security of IoT ecosystems. Below are some recommendations for securing IoT devices:
- Regularly update firmware and software to patch vulnerabilities.
- Use strong, unique passwords for all devices and accounts.
- Segment networks to isolate IoT devices from critical systems.
- Monitor network traffic for suspicious activity.
Tools and Technologies for Enhanced Security
Several tools and technologies can help enhance the security of IoT ecosystems. These include intrusion detection systems (IDS), firewalls, and security information and event management (SIEM) solutions.
For example, the IoT Security Foundation provides guidelines and resources for securing IoT devices. Additionally, companies like Cisco and Palo Alto Networks offer specialized IoT security solutions tailored to enterprise needs.
Popular IoT Security Tools
- Snort: An open-source intrusion detection system.
- Wireshark: A network protocol analyzer for monitoring traffic.
- Qualys: A cloud-based security platform for vulnerability management.
Ensuring Data Privacy in IoT
Data privacy is a critical concern in IoT, as devices often collect sensitive information about users and their environments. To protect user data, organizations must comply with regulations such as the General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA).
Implementing data minimization principles, anonymizing data, and obtaining user consent are effective strategies for ensuring data privacy in IoT ecosystems.
Future Trends in IoT Security
The future of IoT security is shaped by emerging technologies and evolving threats. Some key trends to watch include:
- Artificial Intelligence (AI) and Machine Learning (ML): Enhancing threat detection and response capabilities.
- Blockchain: Providing decentralized and tamper-proof data storage solutions.
- Quantum Computing: Revolutionizing encryption and cybersecurity.
Conclusion and Call to Action
Securing remote IoT connections through P2Psh Android is essential for maintaining the integrity and privacy of data. By understanding the challenges and implementing best practices, organizations can create robust IoT ecosystems that meet the demands of modern technology.
We encourage readers to share their thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our website for more insights into IoT and cybersecurity.
Sources:
- Gartner - IoT Security Spending Forecast
- IoT Security Foundation - Best Practices Guide
- Cisco - IoT Security Solutions