In today's rapidly advancing technological landscape, IoT (Internet of Things) devices are becoming increasingly integral to our daily lives. Whether it's smart homes, industrial automation, or healthcare systems, IoT devices offer unparalleled convenience and efficiency. However, managing these devices securely and effectively requires specialized tools like IoTSH Login CLI. This command-line interface (CLI) tool has emerged as a game-changer for IT professionals and device administrators looking to streamline their IoT device management processes.
IoTSH Login CLI is more than just a tool; it's a powerful solution designed to enhance the security and accessibility of IoT networks. By leveraging this CLI, users can efficiently log in to IoT devices, manage configurations, and monitor device performance with ease. As the number of connected devices continues to grow exponentially, understanding how to utilize IoTSH Login CLI becomes crucial for maintaining robust cybersecurity protocols.
This article will delve into the intricacies of IoTSH Login CLI, offering detailed insights into its features, benefits, and best practices for implementation. Whether you're a seasoned IT professional or a beginner exploring IoT management solutions, this guide will provide the comprehensive knowledge you need to harness the full potential of IoTSH Login CLI.
Read also:Song Kang Child The Journey Of A Rising Kdrama Star
Table of Contents
- What is IoTSH Login CLI?
- Key Features of IoTSH Login CLI
- Benefits of Using IoTSH Login CLI
- Installation and Setup of IoTSH Login CLI
- Common CLI Commands for IoTSH Login
- Security Considerations for IoTSH Login CLI
- Troubleshooting IoTSH Login CLI Issues
- Best Practices for Using IoTSH Login CLI
- Comparison with Other IoT Management Tools
- Future Trends in IoT Device Management
What is IoTSH Login CLI?
IoTSH Login CLI stands for Internet of Things Secure Host Command Line Interface. It is a specialized tool designed to facilitate secure access and management of IoT devices through a command-line interface. Unlike traditional web-based management platforms, IoTSH Login CLI offers a more direct and efficient way to interact with IoT devices, ensuring that users can perform tasks quickly and securely.
Developed with security as a top priority, IoTSH Login CLI employs advanced encryption protocols and authentication mechanisms to safeguard sensitive data. This tool is particularly valuable for IT administrators who need to manage large fleets of IoT devices across various locations. By providing a centralized platform for device management, IoTSH Login CLI simplifies the process of monitoring and maintaining IoT networks.
How IoTSH Login CLI Works
The functioning of IoTSH Login CLI revolves around a series of commands that allow users to interact with IoT devices. These commands enable actions such as logging in, updating firmware, and retrieving device status. The CLI operates through a secure connection, ensuring that all communications between the user and the IoT devices are encrypted and protected from unauthorized access.
- Establishes a secure connection to IoT devices
- Provides a range of commands for device management
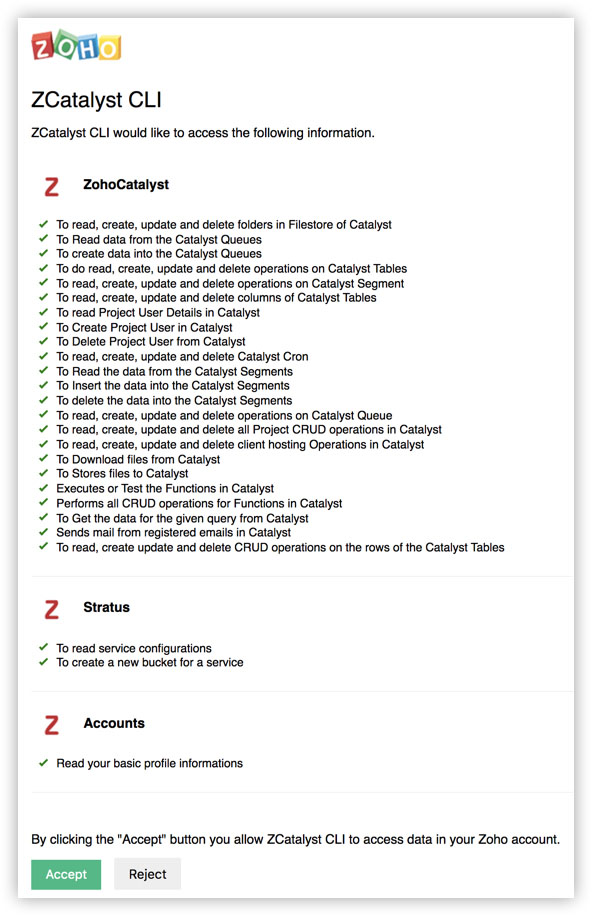
- Supports multiple authentication methods for enhanced security
Key Features of IoTSH Login CLI
IoTSH Login CLI is equipped with several key features that make it an indispensable tool for IoT device management. These features are designed to enhance both the functionality and security of the tool, ensuring that users can manage their IoT devices effectively.
Feature 1: Secure Authentication
One of the standout features of IoTSH Login CLI is its robust authentication system. This feature supports various authentication methods, including multi-factor authentication (MFA), to ensure that only authorized users can access IoT devices.
Feature 2: Comprehensive Command Set
The CLI offers a wide range of commands that cover all aspects of IoT device management. From basic login functions to advanced configuration settings, users can perform virtually any task they need to manage their IoT devices.
Read also:Exploring The Rich Tapestry Of Desi Culture Traditions Cuisine And Influence
Benefits of Using IoTSH Login CLI
Adopting IoTSH Login CLI for IoT device management brings numerous benefits that can significantly enhance the efficiency and security of your IoT network. Below are some of the key advantages of using this tool:
- Improved security through advanced encryption and authentication
- Enhanced productivity with streamlined device management processes
- Cost savings by reducing the need for physical device maintenance
Installation and Setup of IoTSH Login CLI
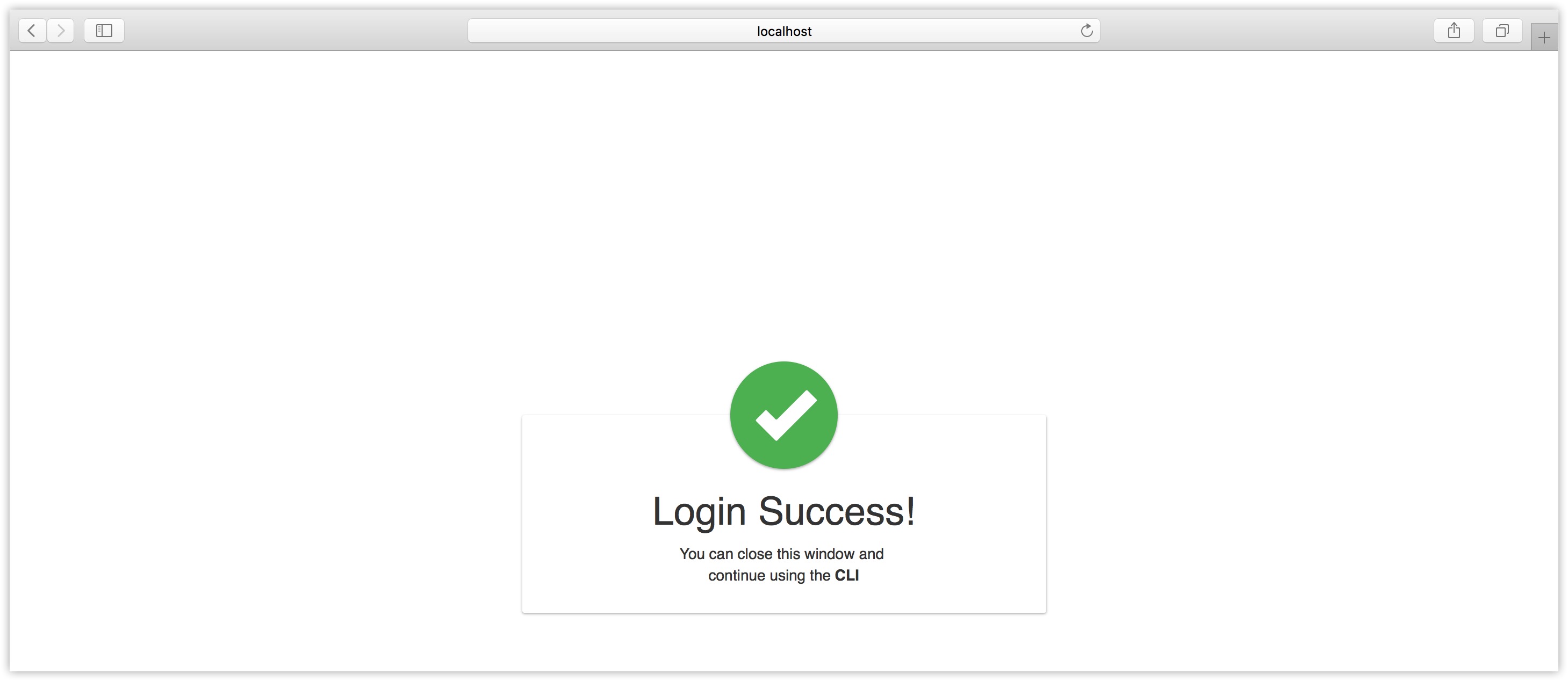
Setting up IoTSH Login CLI involves a straightforward installation process. Users can download the CLI tool from the official website and follow the provided instructions to install it on their systems. Once installed, the CLI can be accessed via the command line, where users can begin configuring their IoT devices.
It's important to note that during the installation process, users should ensure that all necessary dependencies are installed on their systems to avoid any compatibility issues. Additionally, configuring the CLI to connect to IoT devices requires setting up the correct network parameters and authentication credentials.
Steps for Installation
- Download the IoTSH Login CLI installer from the official website
- Run the installer and follow the on-screen instructions
- Configure the CLI with the required network settings
Common CLI Commands for IoTSH Login
Understanding the common CLI commands is essential for effectively using IoTSH Login CLI. Below is a list of some of the most frequently used commands:
login: Logs into an IoT device using specified credentialsstatus: Retrieves the current status of an IoT deviceupdate: Updates the firmware of an IoT device
Security Considerations for IoTSH Login CLI
Security is a critical aspect of IoT device management, and IoTSH Login CLI addresses this concern with several built-in security features. However, users must also take additional steps to ensure the security of their IoT networks. This includes regularly updating the CLI tool, using strong passwords, and enabling multi-factor authentication wherever possible.
Furthermore, it's important to monitor access logs and audit trails to detect any unauthorized access attempts. By implementing these security best practices, users can safeguard their IoT devices against potential threats.
Troubleshooting IoTSH Login CLI Issues
Even with its robust design, IoTSH Login CLI may encounter issues from time to time. Below are some common problems users may face and their respective solutions:
- Connection Errors: Check network settings and ensure the device is reachable
- Authentication Failures: Verify credentials and enable multi-factor authentication
- Command Errors: Review command syntax and consult the official documentation
Best Practices for Using IoTSH Login CLI
To maximize the effectiveness of IoTSH Login CLI, users should adhere to the following best practices:
- Regularly update the CLI tool to the latest version
- Use strong and unique passwords for authentication
- Enable multi-factor authentication for added security
Comparison with Other IoT Management Tools
While IoTSH Login CLI offers a comprehensive solution for IoT device management, it's important to compare it with other tools in the market. Below is a brief comparison:
- IoTSH Login CLI: Offers a secure CLI interface with advanced features
- Other Tools: May provide web-based interfaces with different feature sets
Future Trends in IoT Device Management
The future of IoT device management is exciting, with emerging trends such as AI-driven automation and blockchain-based security solutions. IoTSH Login CLI is well-positioned to adapt to these trends, ensuring that users can continue to manage their IoT devices effectively in an ever-evolving technological landscape.
Conclusion
In conclusion, IoTSH Login CLI is a powerful tool that offers a secure and efficient way to manage IoT devices. By leveraging its key features and following best practices, users can enhance the security and functionality of their IoT networks. We encourage readers to explore the full potential of IoTSH Login CLI and share their experiences with the community. Additionally, feel free to explore other articles on our site for more insights into IoT technology and its applications.