Connecting your IoT devices securely is one of the most critical aspects of modern technology management. As businesses and individuals increasingly rely on IoT devices for various purposes, ensuring secure connections becomes paramount. This guide will provide you with an in-depth understanding of how to securely connect remote IoT devices using a VPC (Virtual Private Cloud) with Raspberry Pi and download the necessary software on Windows.
IoT technology has revolutionized the way we interact with devices, but it also introduces vulnerabilities that need to be addressed. Understanding how to secure your IoT environment is crucial for protecting sensitive data and ensuring uninterrupted operations. This article will walk you through the steps needed to create a secure connection, using a combination of VPC, Raspberry Pi, and Windows.
In this guide, you will learn about the importance of securing IoT devices, the role of VPC in enhancing security, and how Raspberry Pi can be configured as a gateway for secure communication. Additionally, we will discuss how to download and install the necessary software on Windows to manage your IoT devices effectively. Let's dive in!
Read also:Naked Sophie Rain A Dive Into The Allure Of Vulnerability
Table of Contents
- Introduction to IoT Security
- What is VPC?
- Raspberry Pi as an IoT Gateway
- Downloading Software on Windows
- Secure Connection Process
- Best Practices for IoT Security
- Common Security Challenges
- How to Monitor IoT Devices
- Troubleshooting Secure Connections
- Conclusion and Next Steps
Introduction to IoT Security
IoT security is a critical component of any modern technological infrastructure. With billions of connected devices worldwide, securing these devices from cyber threats is more important than ever. The keyword "securely connect remote IoT" highlights the importance of establishing a secure communication channel between devices and the cloud.
IoT devices are often deployed in remote locations, making them vulnerable to unauthorized access. A secure connection ensures that data transmitted between devices and the cloud remains confidential and tamper-proof. This section will explore the fundamental principles of IoT security and why it is essential for protecting your data.
Why IoT Security Matters
IoT security matters because compromised devices can lead to significant financial losses and reputational damage. According to a report by Gartner, the number of IoT devices is expected to exceed 25 billion by 2025. Each of these devices represents a potential entry point for cybercriminals.
- Prevent unauthorized access to sensitive data.
- Protect against malware and ransomware attacks.
- Ensure compliance with industry regulations.
What is VPC?
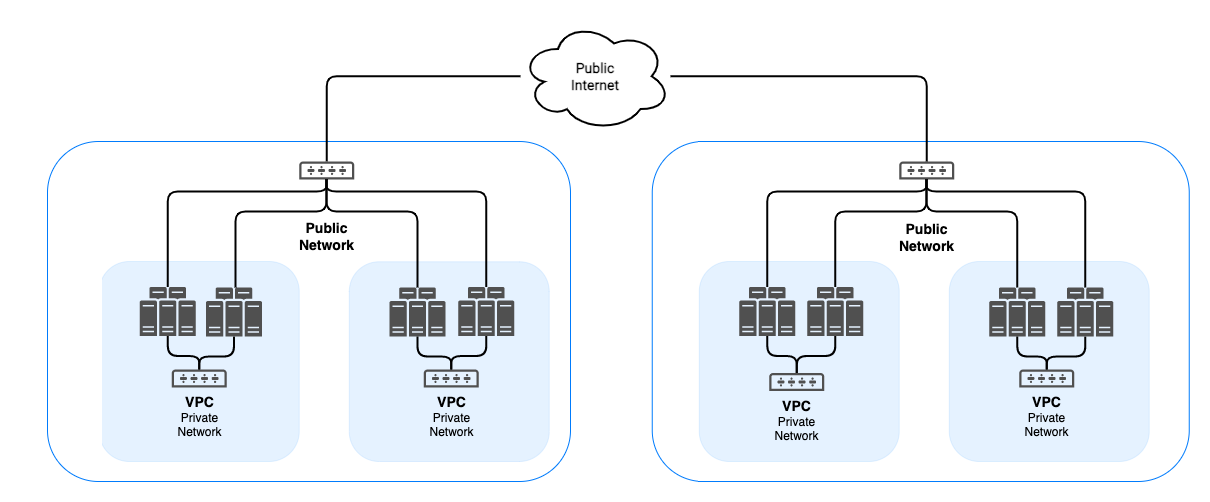
A Virtual Private Cloud (VPC) is a private network environment in the cloud where you can deploy your IoT devices securely. VPCs provide isolation from other networks, ensuring that your devices communicate only with trusted resources. The keyword "VPC Raspberry Pi" emphasizes the role of VPC in securing IoT devices connected via Raspberry Pi.
Key Features of VPC
VPCs offer several features that enhance security and performance:
- Private IP addressing for devices.
- Network access control lists (ACLs) to restrict traffic.
- Subnet configurations for organizing devices.
Raspberry Pi as an IoT Gateway
Raspberry Pi is a versatile single-board computer that can be configured as an IoT gateway. By using Raspberry Pi, you can create a secure bridge between your IoT devices and the cloud. The keyword "Raspberry Pi download" highlights the importance of downloading the necessary software to configure Raspberry Pi for IoT applications.
Read also:The Unstoppable Mark Harmon From Ncis To Hollywood Icon Ndash A True Starrsquos Journey
Steps to Configure Raspberry Pi
Configuring Raspberry Pi as an IoT gateway involves several steps:
- Install the Raspberry Pi operating system.
- Set up network configurations for secure connections.
- Download and install IoT-specific software.
Downloading Software on Windows
To manage your IoT devices effectively, you need to download and install the necessary software on your Windows machine. The keyword "download Windows" emphasizes the importance of having the right tools to manage your IoT environment.
Recommended Software
Here are some recommended software tools for managing IoT devices:
- MQTT client for secure messaging.
- SSH client for remote access.
- Cloud management tools for monitoring.
Secure Connection Process
Establishing a secure connection involves several steps, including configuring firewalls, setting up encryption protocols, and implementing authentication mechanisms. The keyword "securely connect remote IoT" highlights the importance of following a structured process to ensure security.
Encryption Protocols
Encryption protocols such as TLS and SSL are essential for securing data transmissions. These protocols ensure that data remains confidential and tamper-proof during transmission.
Best Practices for IoT Security
Following best practices for IoT security can significantly reduce the risk of cyberattacks. Some of these practices include:
- Regularly updating firmware and software.
- Implementing strong password policies.
- Monitoring device activity for anomalies.
Common Security Challenges
Despite the advancements in IoT technology, several security challenges remain. These challenges include:
- Limited device resources for security features.
- Complexity in managing large-scale IoT deployments.
- Difficulty in implementing consistent security policies.
How to Monitor IoT Devices
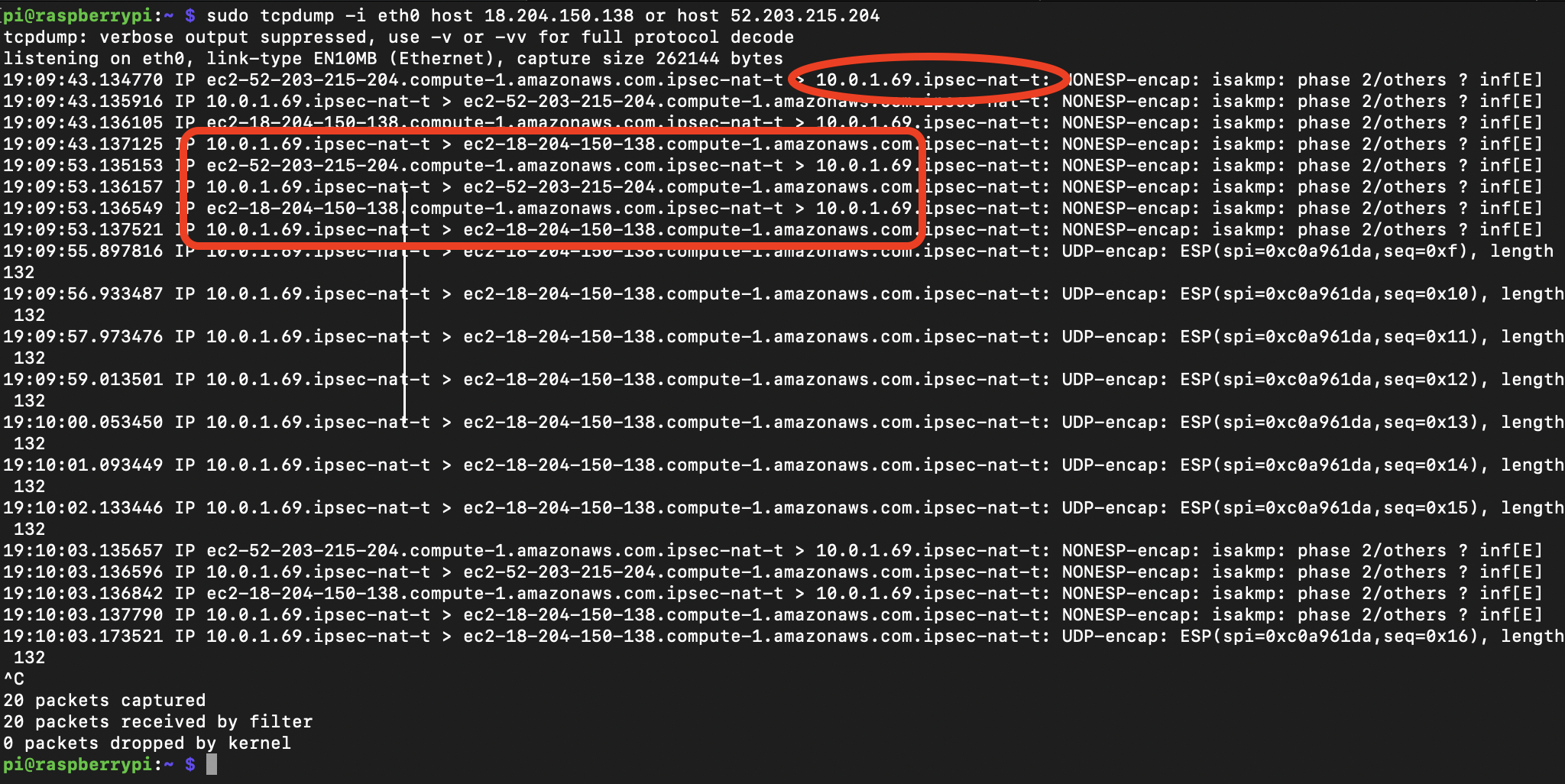
Monitoring IoT devices is crucial for detecting and responding to security threats. Effective monitoring involves:
- Using centralized dashboards for real-time insights.
- Implementing automated alerts for suspicious activities.
- Regularly reviewing logs for potential security breaches.
Troubleshooting Secure Connections
Occasionally, secure connections may fail due to various reasons. Troubleshooting these issues involves:
- Checking network configurations for errors.
- Verifying certificate validity and expiration.
- Testing communication channels for connectivity issues.
Conclusion and Next Steps
In conclusion, securely connecting remote IoT devices using VPC, Raspberry Pi, and Windows is a critical process that requires careful planning and execution. By following the steps outlined in this guide, you can ensure that your IoT environment remains secure and reliable.
We encourage you to take the following actions:
- Review and implement the best practices discussed in this article.
- Explore additional resources for enhancing IoT security.
- Share your feedback and experiences in the comments section below.
Thank you for reading, and we hope this guide has been informative and helpful in your journey to secure your IoT devices. For more articles on technology and security, explore our website further!