In today's interconnected world, securely connect remote IoT VPC has become a critical need for businesses across various industries. As the Internet of Things (IoT) continues to expand, ensuring secure communication between devices and networks is paramount. Without proper security measures, sensitive data and operations can be vulnerable to cyberattacks, leading to significant financial and operational losses.
Organizing a robust infrastructure that incorporates secure remote IoT VPC connections involves understanding the technology's complexities and implementing best practices. This article will delve into the intricacies of creating a secure environment for remote IoT devices, ensuring that data transmission remains protected at all times.
Whether you are a network administrator, IT professional, or decision-maker, this guide will equip you with actionable insights and strategies to enhance your IoT infrastructure's security. Let's explore how to safeguard your remote IoT VPC effectively.
Read also:Does Barron Trump Sing Unveiling The Truth Behind The Rumors
Table of Contents
- Overview of Securely Connect Remote IoT VPC
- Why Is It Important to Securely Connect Remote IoT VPC?
- Understanding the Architecture of IoT VPC
- Common Security Threats in IoT VPC
- Best Practices for Secure IoT VPC Connections
- The Role of Encryption in Securing IoT VPC
- Network Security Measures for IoT VPC
- Effective Device Management for IoT Security
- Monitoring and Auditing IoT VPC Connections
- Future Trends in Secure IoT VPC Connections
Overview of Securely Connect Remote IoT VPC
Connecting remote IoT devices to a Virtual Private Cloud (VPC) involves creating a secure and reliable network infrastructure. A Virtual Private Cloud (VPC) is essentially a private network within a cloud environment, where IoT devices can communicate securely without exposing sensitive data to public networks.
The concept of securely connect remote IoT VPC revolves around ensuring that all data transmitted between IoT devices and the VPC remains encrypted and protected from unauthorized access. This requires a combination of hardware, software, and network security measures.
In this section, we will explore the foundational elements of IoT VPC and how they contribute to secure connections. Additionally, we will discuss the importance of integrating security protocols from the outset of IoT deployment.
Why Is It Important to Securely Connect Remote IoT VPC?
IoT devices are increasingly being used in critical applications, such as healthcare, manufacturing, and transportation. These devices often handle sensitive data, making them prime targets for cybercriminals. A breach in the IoT VPC can lead to severe consequences, including:
- Data theft and misuse
- Operational disruptions
- Financial losses
- Reputation damage
By implementing robust security measures, businesses can mitigate these risks and ensure the integrity of their IoT infrastructure. Securely connecting remote IoT VPC is not just an option but a necessity in today's digital landscape.
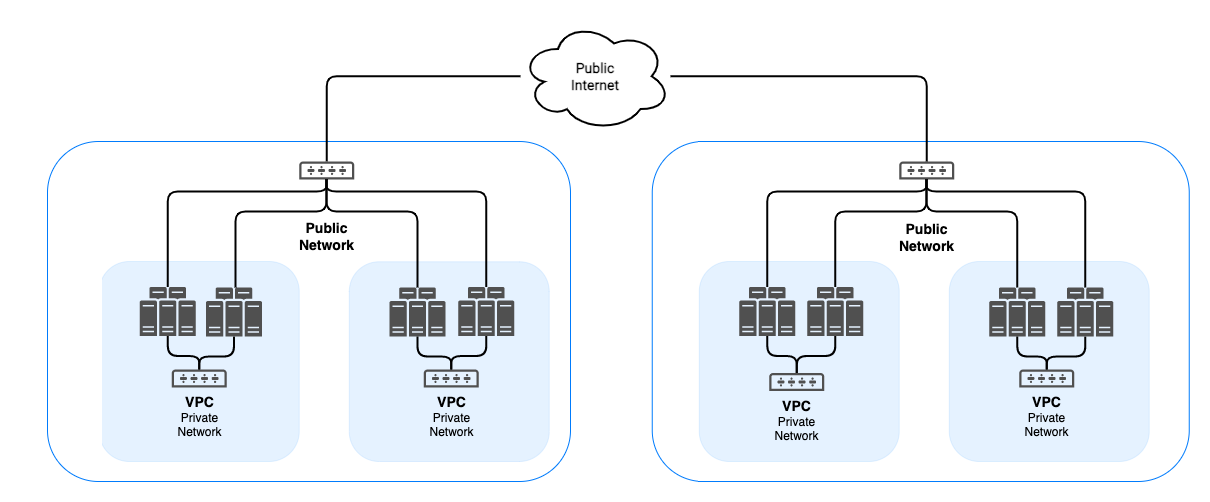
Understanding the Architecture of IoT VPC
Key Components of IoT VPC
The architecture of an IoT VPC typically consists of several key components that work together to ensure secure communication:
Read also:Zach Top Wife Everything You Need To Know About His Life And Relationship
- IoT Devices: Sensors, actuators, and other devices that collect and transmit data.
- Gateways: Intermediate devices that facilitate communication between IoT devices and the cloud.
- Cloud Services: Platforms that process and store IoT data.
- Security Layers: Firewalls, encryption protocols, and authentication mechanisms.
Understanding how these components interact is essential for designing a secure IoT VPC architecture.
Designing a Secure IoT VPC
When designing an IoT VPC, it is crucial to consider factors such as scalability, reliability, and security. Implementing a multi-layered security approach can help protect against potential threats. This includes:
- Segmenting the network to isolate sensitive data.
- Using secure communication protocols like TLS and SSL.
- Implementing access control policies to restrict unauthorized access.
Common Security Threats in IoT VPC
IoT VPC environments face various security threats that can compromise their integrity. Some of the most common threats include:
- DDoS Attacks: Overloading the network with traffic to disrupt operations.
- Man-in-the-Middle (MitM) Attacks: Intercepting and altering communications between devices.
- Malware Infections: Infecting IoT devices with malicious software to gain unauthorized access.
Addressing these threats requires a proactive approach to security management. Regular updates, patches, and monitoring can help mitigate these risks.
Best Practices for Secure IoT VPC Connections
Implementing best practices is essential for ensuring the security of IoT VPC connections. Below are some recommendations:
- Use strong authentication mechanisms, such as multi-factor authentication (MFA).
- Regularly update firmware and software to patch vulnerabilities.
- Conduct security audits and penetration testing to identify weaknesses.
- Limit access to sensitive data by implementing role-based access control (RBAC).
By adhering to these best practices, organizations can significantly enhance the security of their IoT VPC infrastructure.
The Role of Encryption in Securing IoT VPC
Types of Encryption Protocols
Encryption plays a vital role in securing IoT VPC connections. It ensures that data transmitted between devices remains confidential and protected from unauthorized access. Some common encryption protocols used in IoT VPC include:
- TLS (Transport Layer Security): Provides secure communication over a network.
- SSL (Secure Sockets Layer): Encrypts data between a web server and a browser.
- AES (Advanced Encryption Standard): Offers robust encryption for data at rest.
Choosing the right encryption protocol depends on the specific requirements of the IoT application.
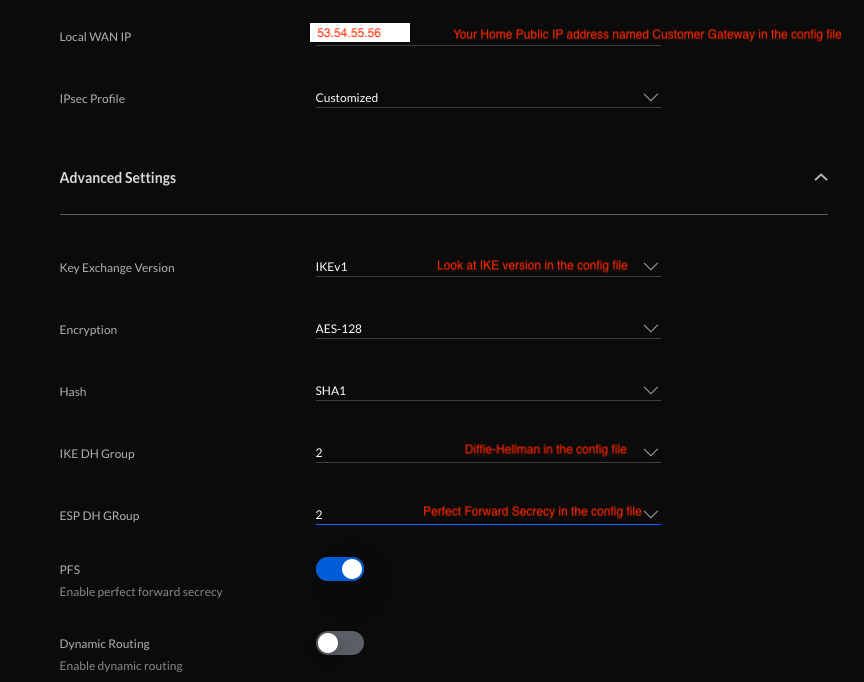
Implementing Encryption in IoT VPC
Implementing encryption in IoT VPC involves several steps, including:
- Selecting appropriate encryption algorithms based on security needs.
- Configuring devices and gateways to support encryption protocols.
- Monitoring encryption keys to ensure their security and validity.
Network Security Measures for IoT VPC
Network security is a critical aspect of securing IoT VPC connections. Implementing robust network security measures can help protect against unauthorized access and cyberattacks. Some effective strategies include:
- Using firewalls to filter incoming and outgoing traffic.
- Implementing intrusion detection and prevention systems (IDPS).
- Segmenting the network to isolate critical components.
These measures, when combined with encryption and authentication protocols, form a comprehensive security framework for IoT VPC.
Effective Device Management for IoT Security
Importance of Device Management
Effective device management is crucial for maintaining the security of IoT VPC. It involves monitoring, updating, and maintaining IoT devices throughout their lifecycle. Key aspects of device management include:
- Tracking device inventory and firmware versions.
- Implementing automated updates and patches.
- Enforcing security policies on all devices.
By managing devices effectively, organizations can reduce the risk of security breaches and ensure smooth operations.
Tools for Device Management
Several tools and platforms are available for managing IoT devices securely. These tools offer features such as:
- Remote device configuration and updates.
- Real-time monitoring and alerts.
- Compliance reporting and audits.
Monitoring and Auditing IoT VPC Connections
Monitoring and auditing IoT VPC connections is essential for detecting and responding to security incidents promptly. Effective monitoring involves:
- Tracking network activity and device behavior.
- Identifying anomalies and potential threats.
- Generating alerts for suspicious activities.
Auditing, on the other hand, involves reviewing security policies and procedures to ensure compliance with industry standards and regulations.
Future Trends in Secure IoT VPC Connections
The field of IoT security is continually evolving, with new technologies and trends emerging to address emerging challenges. Some future trends in secure IoT VPC connections include:
- Artificial intelligence (AI) and machine learning (ML) for threat detection and response.
- Blockchain for secure data sharing and authentication.
- Quantum cryptography for advanced encryption.
Staying informed about these trends will help organizations stay ahead of potential security threats and maintain a secure IoT VPC infrastructure.
Kesimpulan
Securing remote IoT VPC connections is a critical task that requires a comprehensive approach. By understanding the architecture, addressing common security threats, and implementing best practices, organizations can protect their IoT infrastructure from cyberattacks and ensure the integrity of their data.
We encourage readers to take action by reviewing their current IoT security measures and implementing the strategies discussed in this article. Additionally, feel free to share your thoughts and experiences in the comments section below. For more insights on IoT security, explore our other articles on the subject.