In the rapidly evolving world of IoT, understanding how to deploy RemoteIoT solutions behind a firewall is essential for maintaining security and functionality. Whether you're a developer, IT professional, or business owner, knowing the intricacies of RemoteIoT behind firewall examples can significantly enhance your network's security and performance. This article delves into the complexities of RemoteIoT behind firewalls, offering practical insights and actionable advice.
As the Internet of Things (IoT) continues to expand, the challenge of securing connected devices grows increasingly complex. RemoteIoT solutions, which allow devices to communicate securely from remote locations, play a crucial role in modern IoT deployments. However, ensuring these devices operate seamlessly behind firewalls requires a thorough understanding of networking principles and security protocols.
This guide explores various RemoteIoT behind firewall examples, offering solutions for common challenges and best practices for secure IoT implementation. By the end of this article, you'll have a comprehensive understanding of how to deploy RemoteIoT solutions effectively while maintaining robust security measures.
Read also:Discovering Iman Benson A Rising Star In The Entertainment Industry
Table of Contents
- Introduction to RemoteIoT Behind Firewalls
- Understanding Firewalls in IoT Context
- Benefits of RemoteIoT Behind Firewalls
- Common Challenges with RemoteIoT Deployments
- RemoteIoT Behind Firewall Examples
- Enhancing Security for RemoteIoT Solutions
- Networking Considerations for RemoteIoT
- Tools and Technologies for RemoteIoT
- Best Practices for RemoteIoT Deployment
- Conclusion and Call to Action
Introduction to RemoteIoT Behind Firewalls
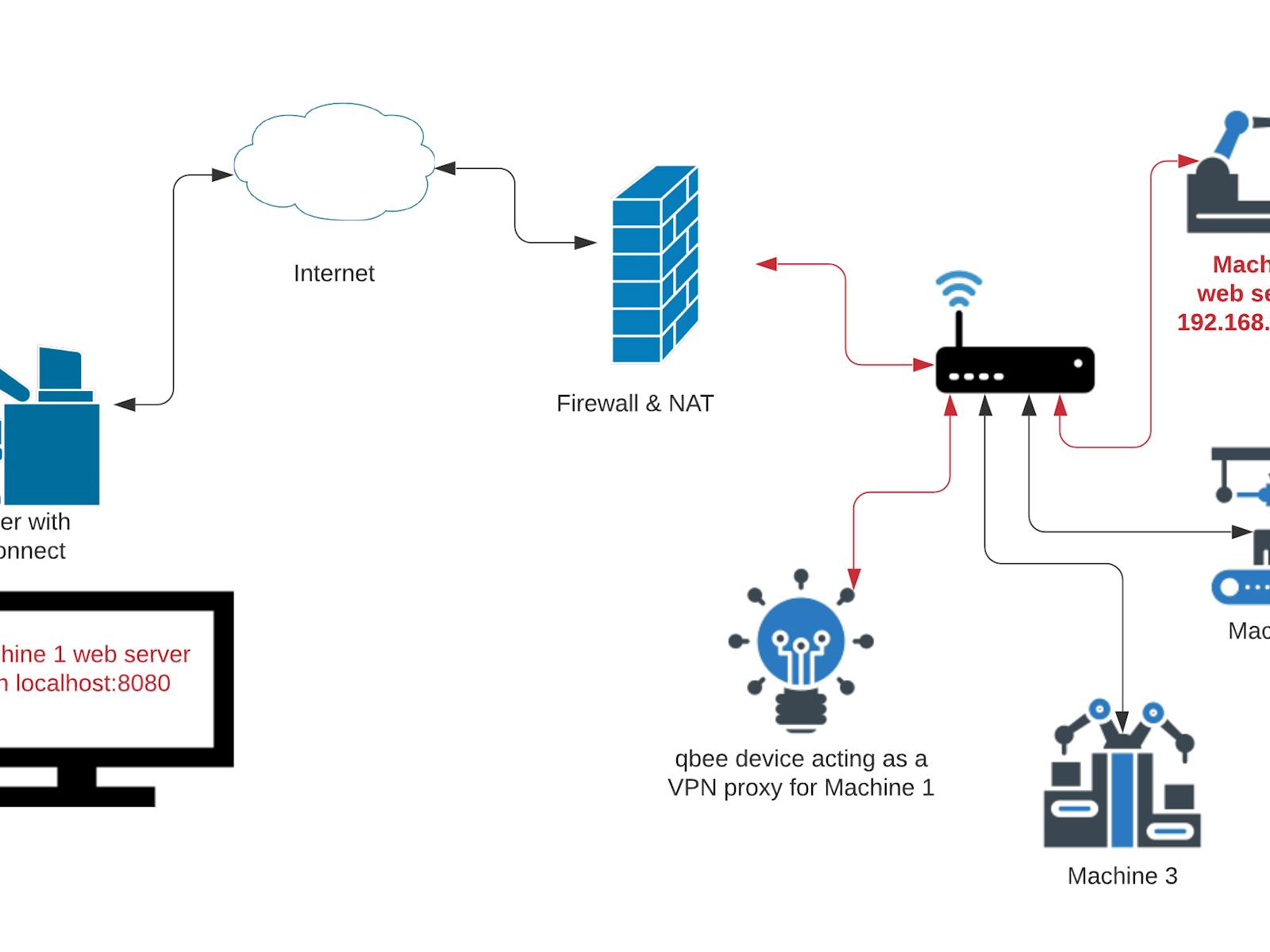
Deploying RemoteIoT solutions behind firewalls is a critical aspect of modern IoT architecture. Firewalls act as a barrier between internal networks and external threats, ensuring that only authorized traffic passes through. In the context of IoT, this means configuring firewalls to allow communication between remote devices and central servers while blocking unauthorized access.
RemoteIoT behind firewall examples illustrate how organizations can maintain secure communication channels without compromising network security. By implementing robust firewall rules and leveraging advanced networking technologies, businesses can ensure that their IoT devices remain connected and functional, even in highly secure environments.
Understanding Firewalls in IoT Context
What is a Firewall?
A firewall is a security system that monitors and controls incoming and outgoing network traffic based on predetermined security rules. In the IoT ecosystem, firewalls play a vital role in protecting devices from cyber threats while enabling seamless communication.
Types of Firewalls
There are several types of firewalls, each suited to different IoT deployment scenarios:
- Packet Filtering Firewalls: Examine packets at the network layer and decide whether to allow or block them based on source and destination IP addresses, ports, and protocols.
- Stateful Inspection Firewalls: Track active connections and use this state information to make more informed decisions about allowing or blocking traffic.
- Application-Level Gateways: Operate at the application layer, providing deep inspection of application-specific traffic.
Benefits of RemoteIoT Behind Firewalls
Deploying RemoteIoT solutions behind firewalls offers numerous benefits, including enhanced security, improved network performance, and better control over device communications. By isolating IoT devices within a secure network, organizations can reduce the risk of unauthorized access and data breaches.
Read also:Laura Bretan Net Worth A Rising Stars Journey To Success
Additionally, firewalls enable granular control over which devices and applications can communicate with each other, ensuring that only trusted entities have access to sensitive data. This level of control is particularly important in industries such as healthcare, finance, and manufacturing, where data security is paramount.
Common Challenges with RemoteIoT Deployments
Network Complexity
One of the primary challenges in RemoteIoT deployments is managing the complexity of modern networks. As the number of connected devices grows, so does the need for robust network infrastructure capable of handling increased traffic loads.
Security Threats
Cyber threats pose a significant risk to IoT deployments, particularly when devices are connected to the internet. Firewalls help mitigate these risks by filtering out malicious traffic and blocking unauthorized access attempts. However, configuring firewalls correctly requires a deep understanding of networking principles and security protocols.
RemoteIoT Behind Firewall Examples
Example 1: Industrial IoT Deployment
In industrial settings, RemoteIoT solutions are often used to monitor and control machinery in remote locations. By deploying firewalls between IoT devices and central servers, organizations can ensure that only authorized personnel have access to sensitive data and control systems.
Example 2: Smart Home Automation
Smart home devices, such as thermostats, security cameras, and lighting systems, rely on secure communication channels to function properly. Firewalls can be configured to allow only trusted devices to connect to the home network, reducing the risk of unauthorized access.
Enhancing Security for RemoteIoT Solutions
Securing RemoteIoT deployments involves implementing a multi-layered approach to cybersecurity. This includes using strong authentication mechanisms, encrypting data in transit, and regularly updating firmware and software to address known vulnerabilities.
Additionally, organizations should conduct regular security audits and penetration tests to identify potential weaknesses in their network infrastructure. By staying proactive and addressing security concerns early, businesses can minimize the risk of cyber attacks and data breaches.
Networking Considerations for RemoteIoT
Bandwidth Requirements
RemoteIoT solutions require sufficient bandwidth to ensure reliable communication between devices and servers. Organizations should carefully evaluate their network infrastructure to ensure it can handle the expected traffic load without compromising performance.
Latency and Reliability
Latency and reliability are critical factors in IoT deployments, particularly for applications that require real-time data processing. By optimizing network configurations and leveraging advanced technologies such as edge computing, businesses can reduce latency and improve overall system reliability.
Tools and Technologies for RemoteIoT
Several tools and technologies are available to support RemoteIoT deployments behind firewalls. These include:
- Network Monitoring Tools: Enable organizations to monitor network traffic and identify potential security threats in real-time.
- Firewall Management Software: Simplifies the process of configuring and managing firewall rules, ensuring consistent security policies across the network.
- Encryption Protocols: Protect sensitive data by encrypting it during transmission, making it unreadable to unauthorized parties.
Best Practices for RemoteIoT Deployment
To ensure successful RemoteIoT deployments behind firewalls, organizations should follow these best practices:
- Conduct thorough risk assessments to identify potential vulnerabilities in the network infrastructure.
- Implement strong authentication mechanisms to verify the identity of devices and users.
- Regularly update firmware and software to address known vulnerabilities and improve system performance.
- Monitor network traffic continuously to detect and respond to security threats in real-time.
Conclusion and Call to Action
In conclusion, deploying RemoteIoT solutions behind firewalls is essential for maintaining secure and reliable IoT deployments. By understanding the intricacies of RemoteIoT behind firewall examples and following best practices for secure implementation, organizations can protect their networks from cyber threats while enabling seamless communication between devices.
We invite you to share your thoughts and experiences with RemoteIoT deployments in the comments section below. Additionally, feel free to explore other articles on our site for more insights into IoT security and networking. Together, we can build a safer and more connected world.
Data Sources: